Almost Half of Industrial Computers in the Middle East Were Attacked in the First Half of 2017: Kaspersky

A recent study by Kaspersky Lab entitled “Threat Landscape for Industrial Automation Systems in H1 2017” showed that in the first half of the year, manufacturing companies were the most susceptible to cyber threats: their ICS computers accounted for about one third of all attacks, according to the Kaspersky Lab report “Threat Landscape for Industrial Automation Systems in H1 2017”. The peak of attackers’ activity was registered in March, after which the proportion of computers attacked gradually declined from April to June.
During the first six months of the year, Kaspersky Lab products blocked attack attempts on 48.4% of ICS computers in the Middle East from which we received anonymized information, globally totaling several tens of thousands. Among all countries in the Middle East region, the greatest change in the percentage of ICS computers attacked, compared to the previous six months, was in Saudi Arabia – the figure for the country increased by 6.4% compared to H2 2016.. The majority of them were in manufacturing companies that produce various materials, equipment and goods. Other highly-affected industries include engineering, education and mining. ICS computers in energy companies in the Middle East accounted for almost 9% of all attacks.
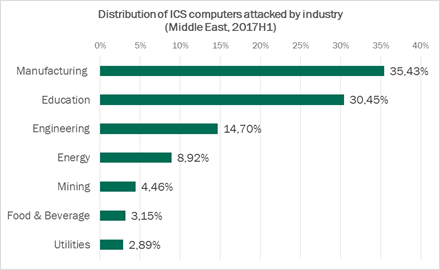
Distribution of ICS computers attacked by industry in the Middle East region by industry, H1 2017
While the top three countries worldwide with attacked industrial computers - Vietnam (71%), Algeria (67.1%) and Morocco (65.4%) remained the same, researchers detected an increase in the percentage of systems attacked in China (57.1%), which came fifth, according to the data released by Kaspersky Lab. As for the Middle East region, Iran (55.3%), Iraq (51.8%) and Saudi Arabia (51.8%) were the most attacked while Egypt (51,6%) kept 4th place, The UEA hold 9th place in the local rating with 43.8% of ICS computers attacked. Experts also discovered that the main source of threats was the Internet: attempts to download malware or access known malicious or phishing web resources were blocked on 25.3% of ICS computers compared to 20.4 globally. The reason of the high statistics for this type of infection lies in interfaces between corporate and industrial networks, availability of limited Internet access from industrial networks, and connection of computers on industrial networks to the Internet via mobile phone operators’ networks.
In total, Kaspersky Lab detected about 3,000 different modifications of malware on industrial automation systems in the Middle East in the first six months of 2017, belonging to more than 650 different families.
Ransomware Attacks
In the first half of the year the world has been facing a ransomware epidemic, which also affected industrial companies. Based on the research from Kaspersky Lab ICS CERT, the number of unique ICS computers attacked by encryption Trojans increased significantly and had tripled by June. Overall, experts discovered encryption ransomware belonging to 33 different families. Most of the encryption Trojans were distributed through spam emails disguised as part of the business communication, with either malicious attachments or links to malware downloaders.
The main ransomware statistics from the H1, 2017 report include:
- 0.3% of computers in the industrial infrastructure of organizations in the Middle East and 0.5 globally were attacked by encryption ransomware at least once.
- ICS computers in 63 countries across the globe faced numerous encryption ransomware attacks, the most notorious of which were the WannaCry and ExPetr campaigns.
- The WannaCry epidemic ranked highest among encryption ransomware families, with 13.4% of all computers in industrial infrastructure attacked. The most affected organizations included healthcare institutions and the government sector.
- ExPetr was another notorious encryption ransomware campaign from the first half of the year, with at least 50% of the companies attacked being from manufacturing, and Oil & Gas industries.
- The Top 10 most widespread encryption Trojan families include other ransomware families, such as Locky and Cerber, operating since 2016 and since that time have earned the highest profit for cybercriminals.
“In the first half of the year we've seen how weakly protected industrial systems are: pretty much all of the affected industrial computers were infected accidentally and as the result of attacks targeted initially at home users and corporate networks. In this sense, the WannaCry and ExPetr destructive ransomware attacks proved indicative, leading to the disruption of enterprise production cycles around the world, as well as logistical failures, and forced downtime in the work of medical institutions. The results of such attacks can provoke intruders into further actions. Since we are already late with preventive measures, companies should think about proactive protective measures now to avoid ‘firefighting’ in future.” says Evgeny Goncharov, Head of Critical Infrastructure Defense Department, Kaspersky Lab.
In order to protect the ICS environment from possible cyber-attacks, Kaspersky Lab ICS CERT recommends the following:
- Take an inventory of running network services with special emphasis on services that provide remote access to file system objects.
- Audit ICS component access isolation, the network activity in the enterprise’s industrial network and at its boundaries, policies and practices related to using removable media and portable devices.
- Verify the security of remote access to the industrial network as a minimum, and reduce or completely eliminate the use of remote administration tools as a maximum.
- Keep endpoint security solutions up-to-date.
- Use advanced methods of protection: deploy tools that provide network traffic monitoring and the detection of cyberattacks on industrial networks.
Kaspersky Lab will be showcasing its next generation Industrial Security solutions during GITEX Technology Week 2017. Join us on stand C1-1 in Hall 1 (Network & Security) to know more about the report from local experts.
Read a summary of the Kaspersky Lab ICS CERT report for H1 2017 on Securelist.com.
The full report is available on Kaspersky Lab ICS CERT website.
Background Information
Kaspersky
Kaspersky is a global cybersecurity company founded in 1997. Kaspersky’s deep threat intelligence and security expertise is constantly transforming into innovative security solutions and services to protect businesses, critical infrastructure, governments and consumers around the globe. The company’s comprehensive security portfolio includes leading endpoint protection and a number of specialized security solutions and services to fight sophisticated and evolving digital threats. Over 400 million users are protected by Kaspersky technologies and we help 250,000 corporate clients protect what matters most to them. Learn more at www.kaspersky.com.






